Key Transfer Protocol
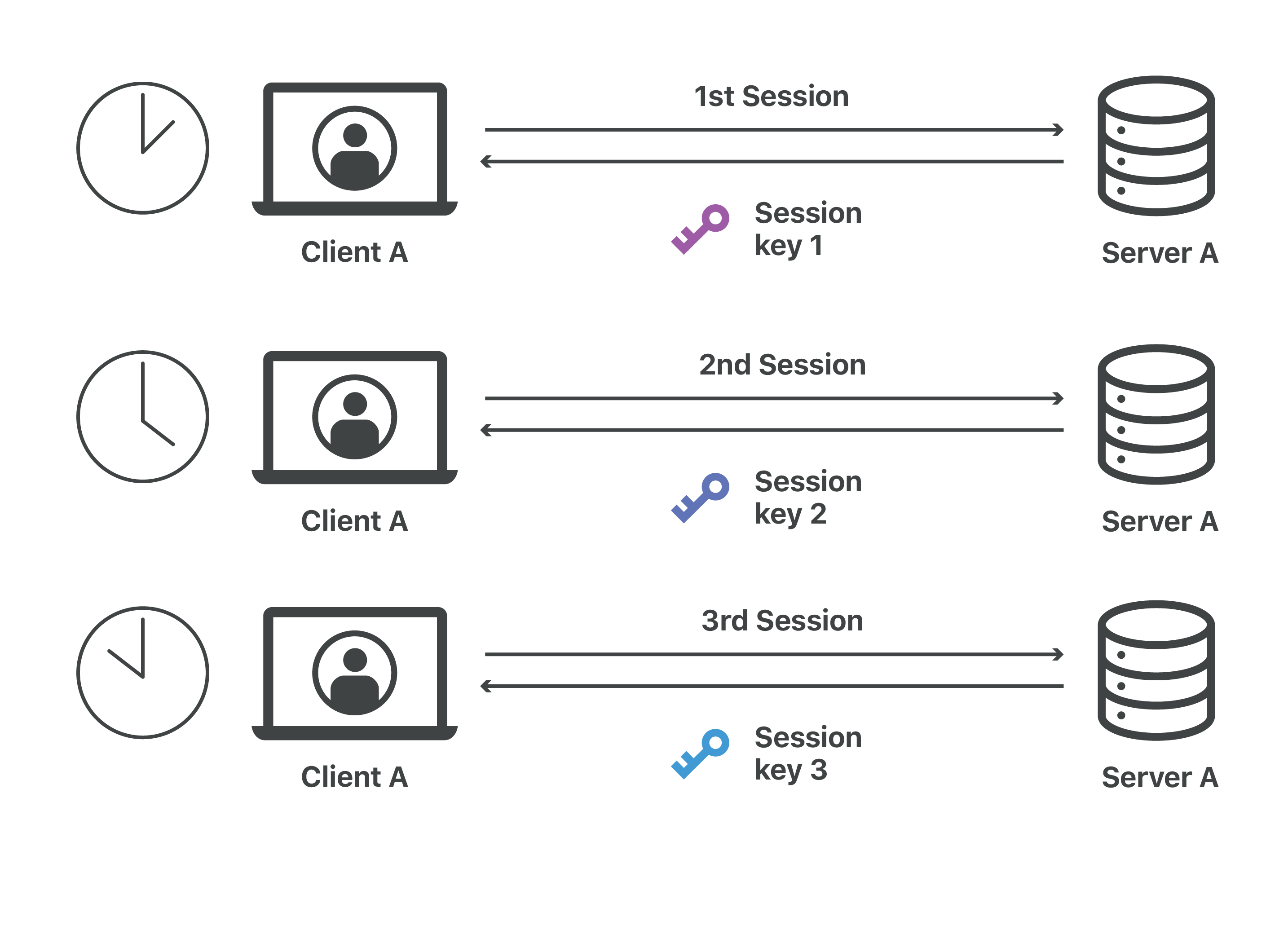
To deal with secure key exchange a three-way key exchange and agreement protocol.
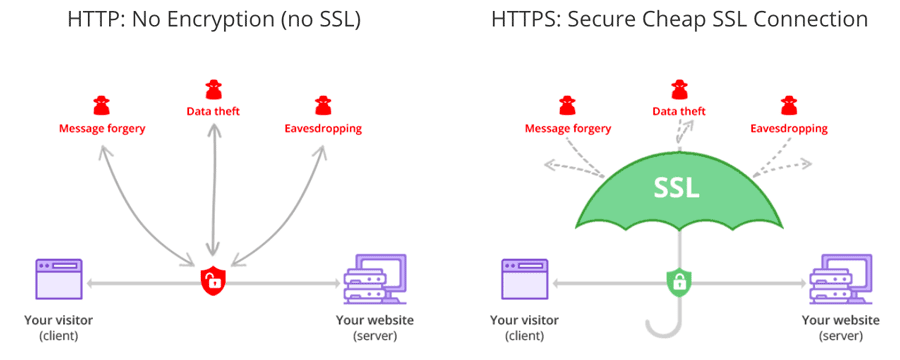
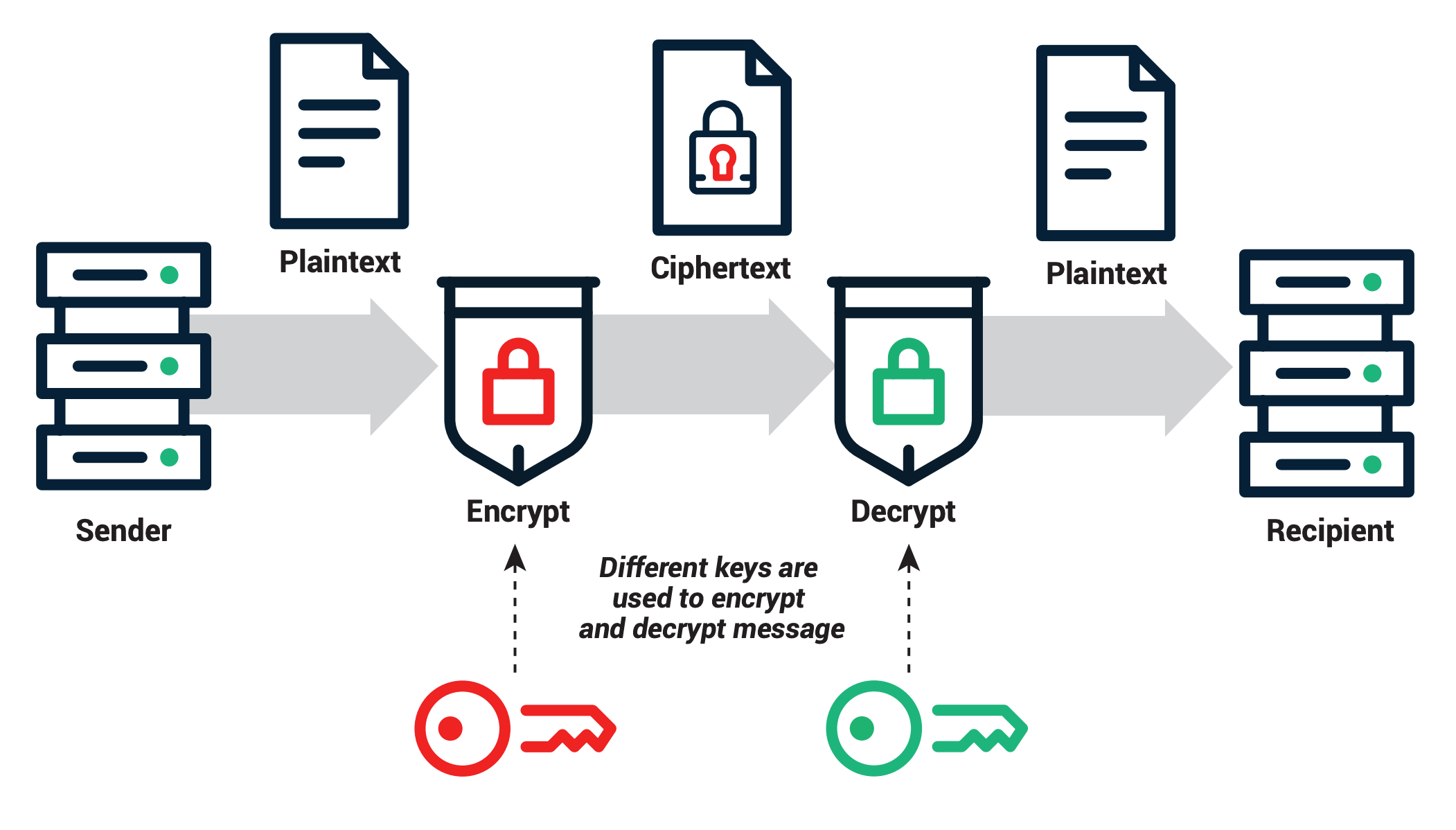
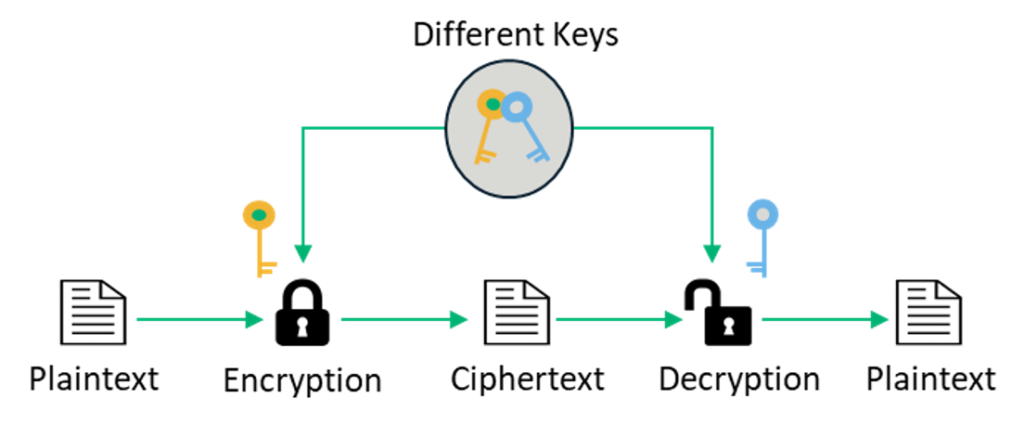
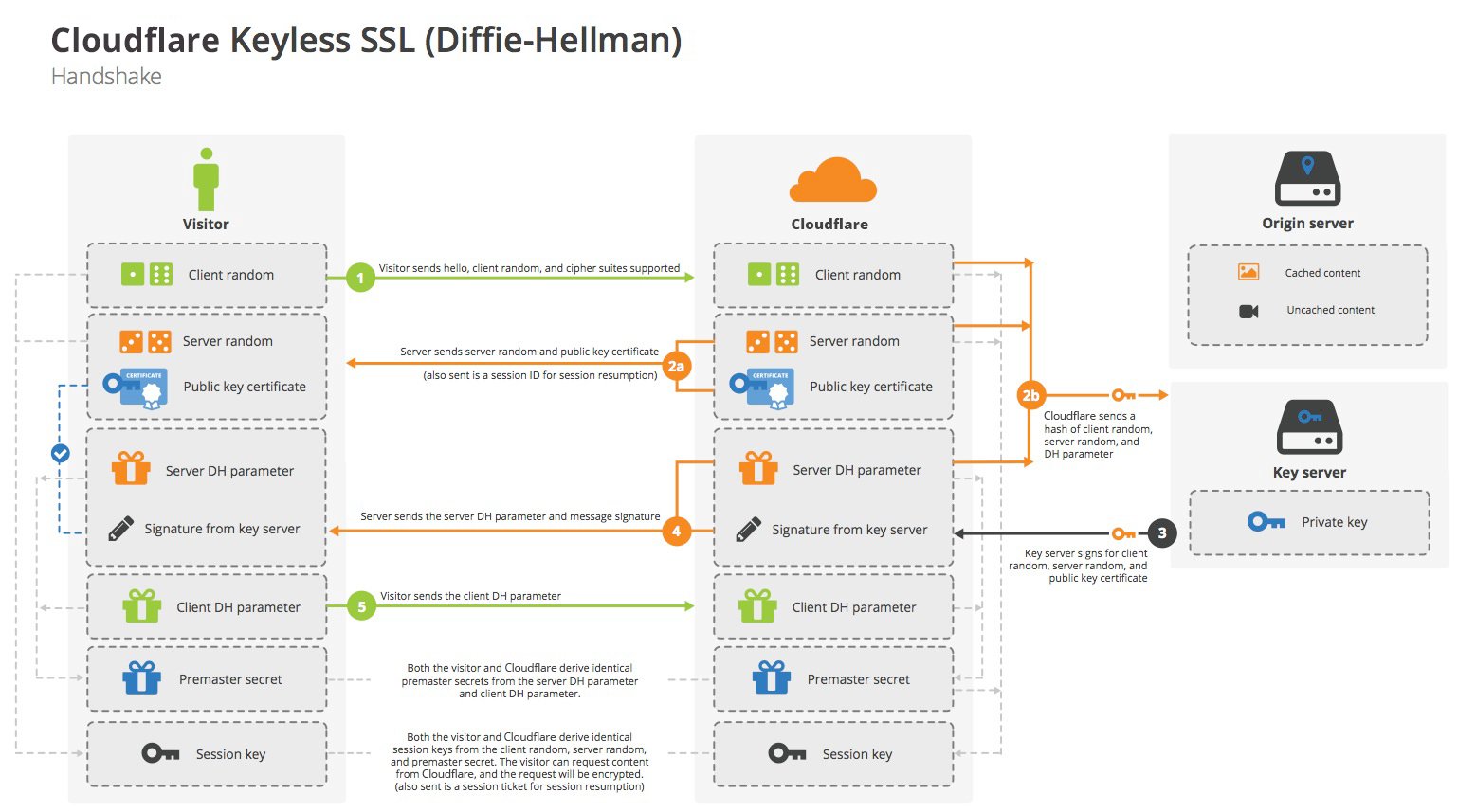
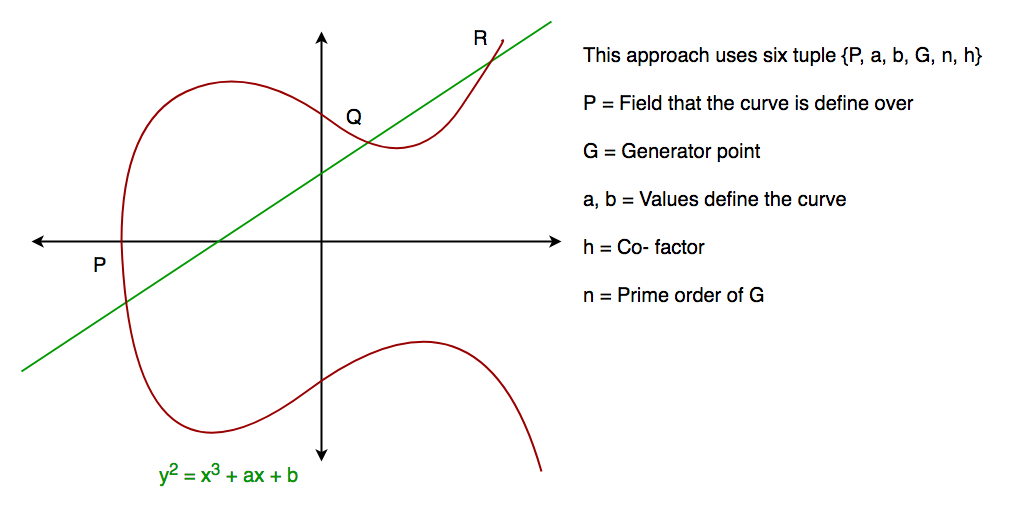
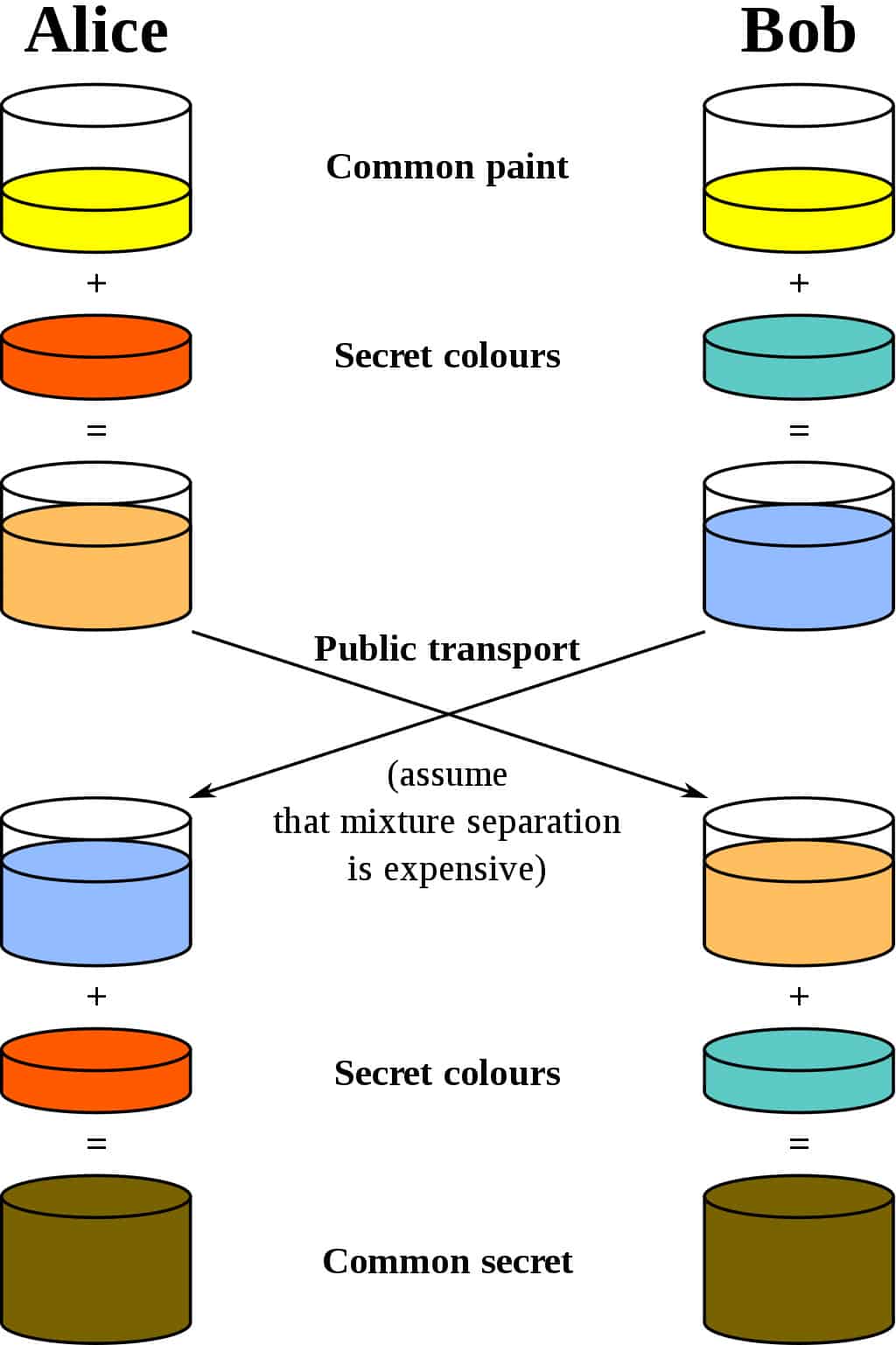
Key transfer protocol. The key exchange protocol is considered an important part of cryptographic mechanism to protect secure end-to-end communications. Both the data of the established connection and the transferred data are encrypted with keys using the SSH protocol. An example of key exchange protocol is the Diffie and Hellman key exchange DIF 06 STA 10 which is known to be vulnerable to attacks.
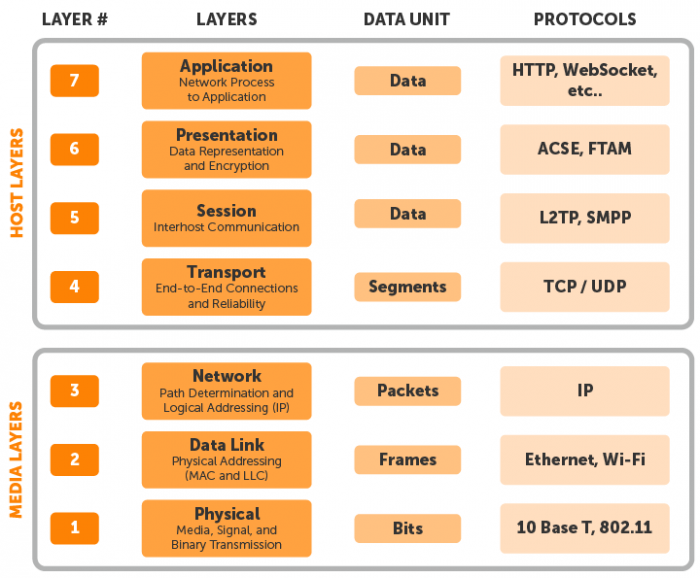
FTP users may authenticate themselves with a clear-text sign-in protocol normally in the form of a. 10252012 A variety of secure communication standards that use public key technology have been developed including Hypertext Transfer Protocol SHTTP IP Security IPSec PPTP and L2TP. This protocol ensures encrypted data transfer to and from client and server systems over a single connection.
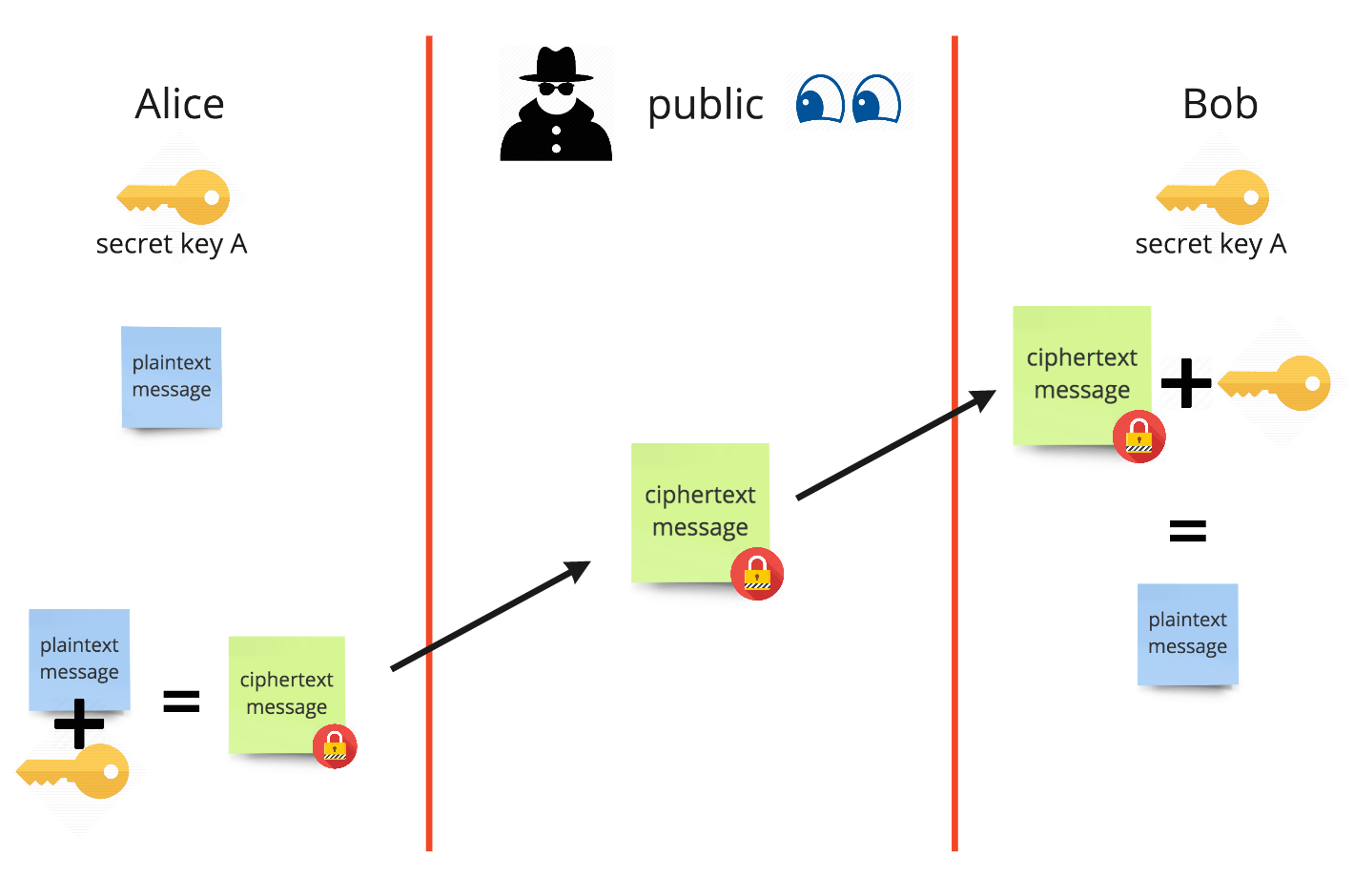
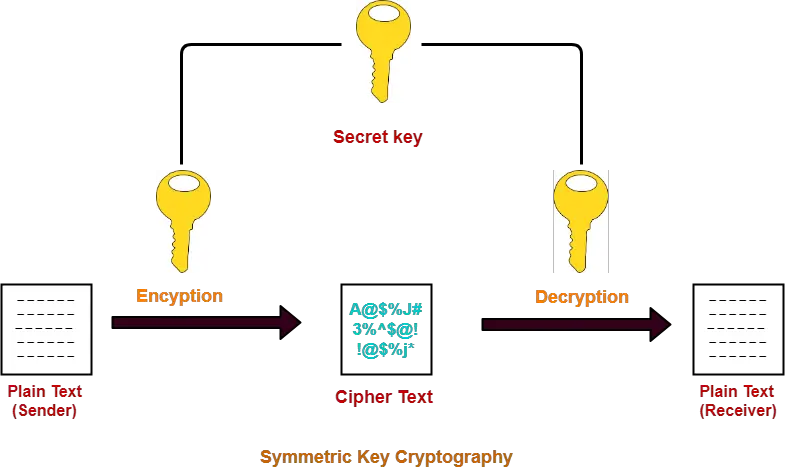
The keys may be identical or there may be a simple transformation to go between the two keys. Keys may be created on a server and then retrieved possibly wrapped by other keys. The leading general-purpose secure web communication protocols are SSL 30 and the open TLS protocol that is based on SSL.
Once an SSH key has been created the ssh-copy-id command can be used to install it as an authorized key on the server. The protocol enables users to securely exchange secret keys even if an opponent is monitoring that communication channel. It runs over the SSH protocol.
TFTP works a little bit differently. SSH File Transfer Protocol SFTP. The keys in practice represent a shared secret between two or more parties that can be used to maintain a private information link.
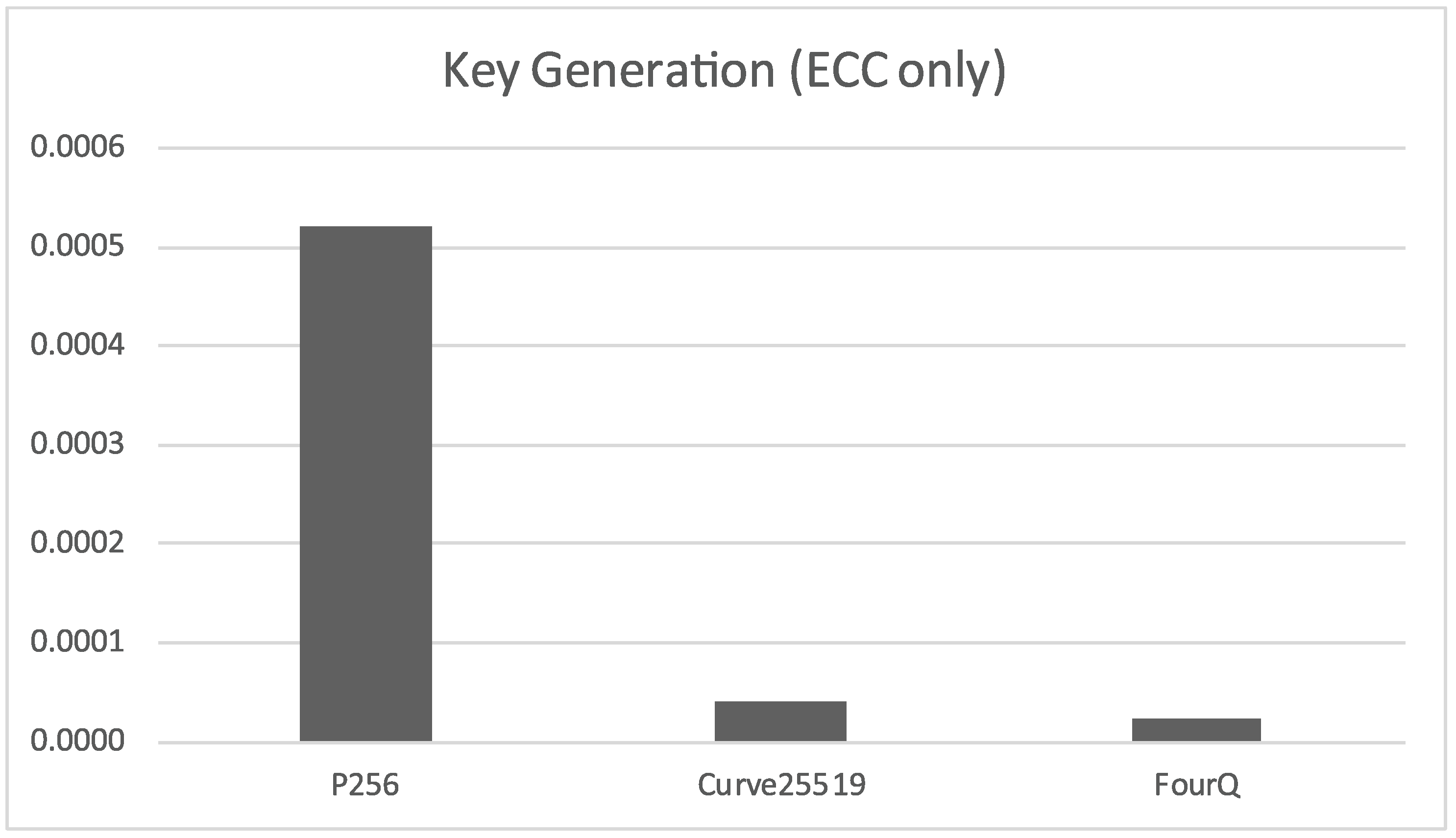
In this paper an efficient key generation and key transfer protocol has been proposed where KGC can broadcast group key information to all group members in a secure way. Ssh-copy-id -i sshmykey userhost. Copy the key to a server.