Transfer Gpg Key
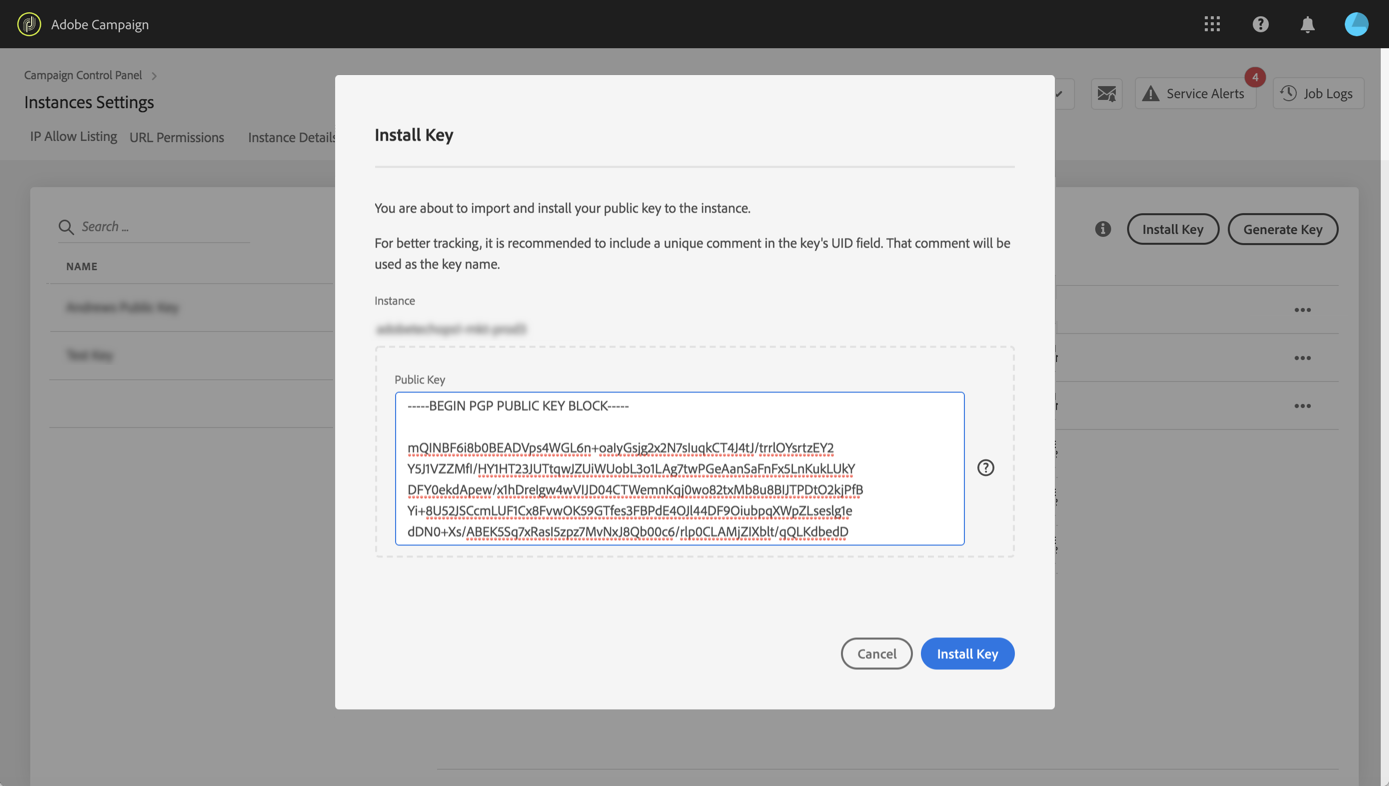
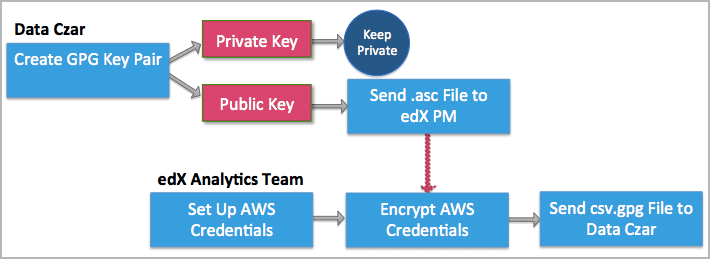
If the destination has their own GPG key you can encrypt the file so that only they can open it.
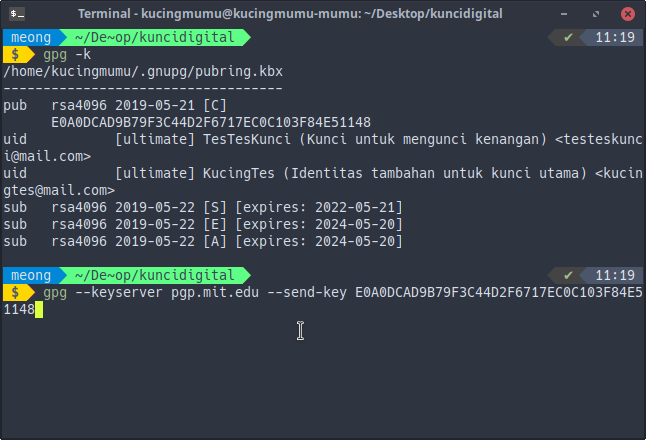
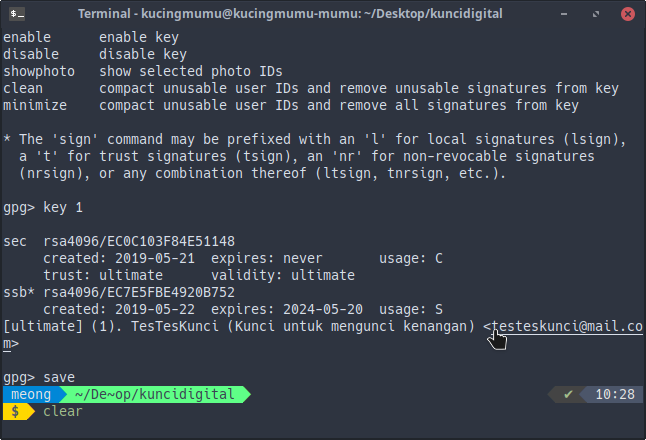
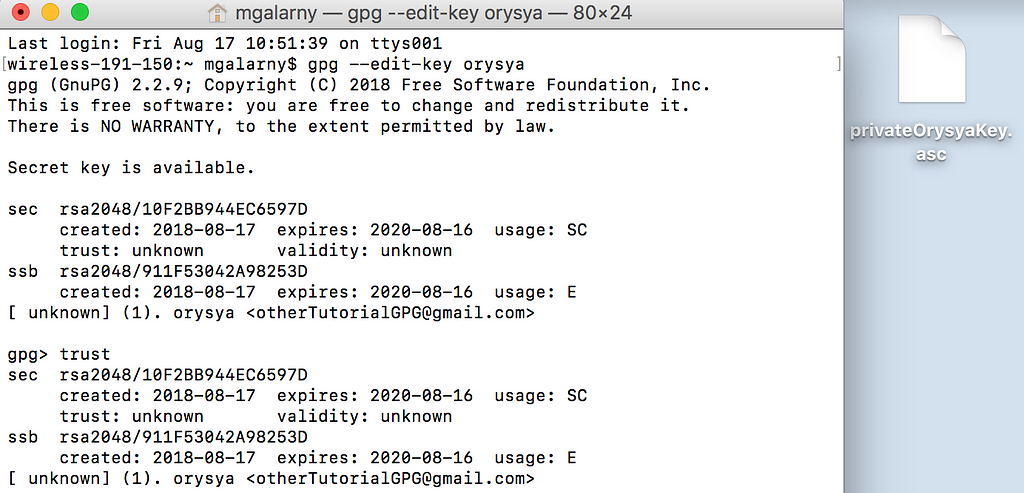
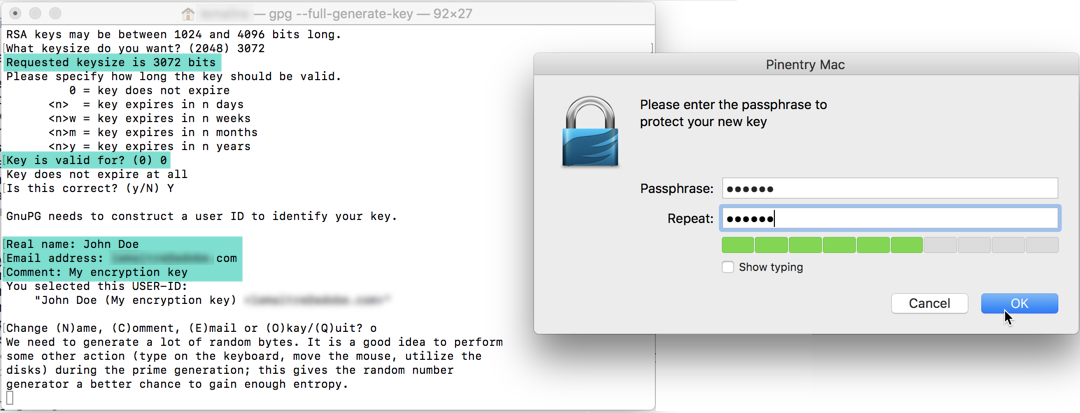
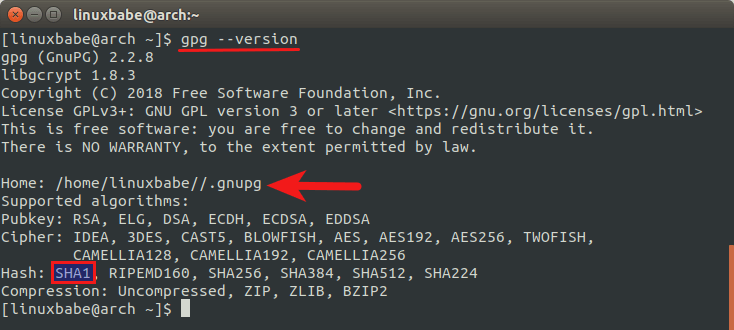
Transfer gpg key. Ssh othermachine gpg --export-secret-key SOMEKEYID gpg --import If gpg isnt in one of the default places on the remote machine eg its in optlocalbin on a Mac youll have to give its full path to ssh or symlink it into one of the standard places such as usrlocalbin. Select SSH and GPG keys. Adding a default signing key is straight-forward.
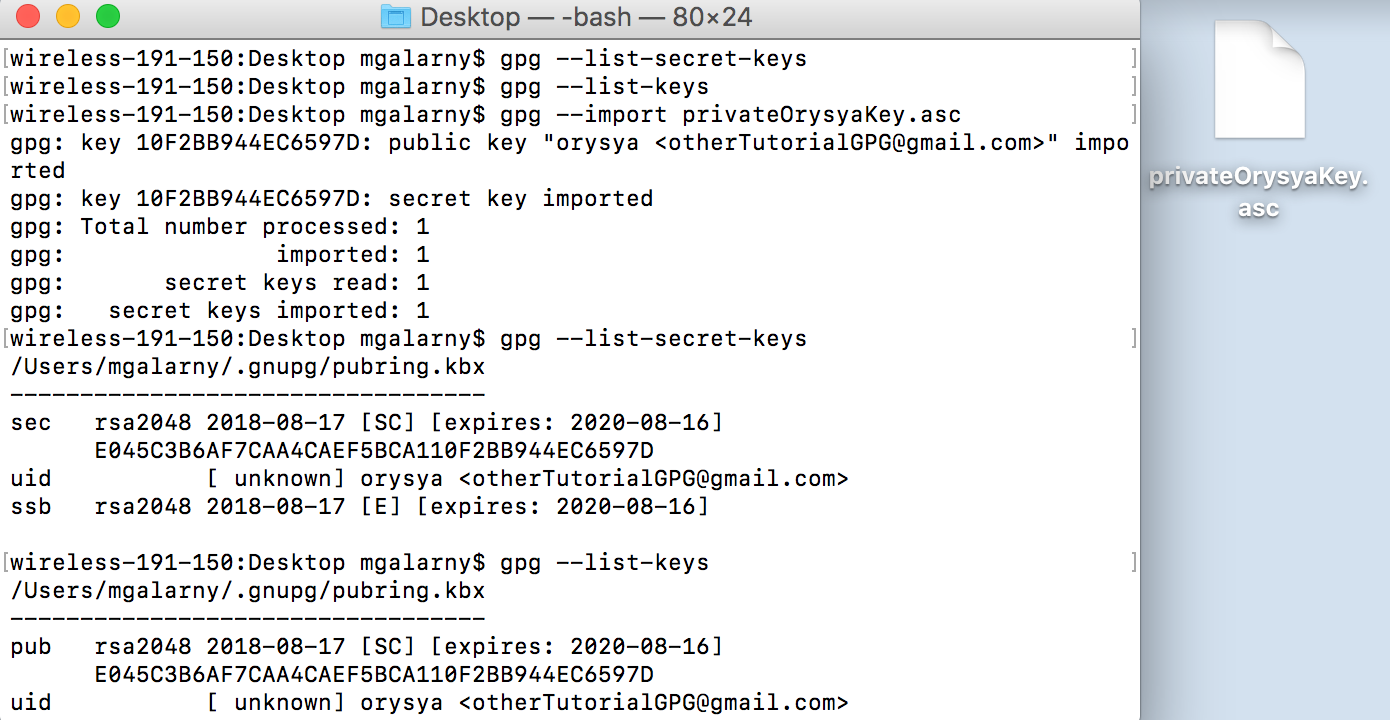
Directory homeusergnupg created gpg. Gpg --import leehanxue. Options in homeusergnupggpgconf are not yet active during this run gpg.
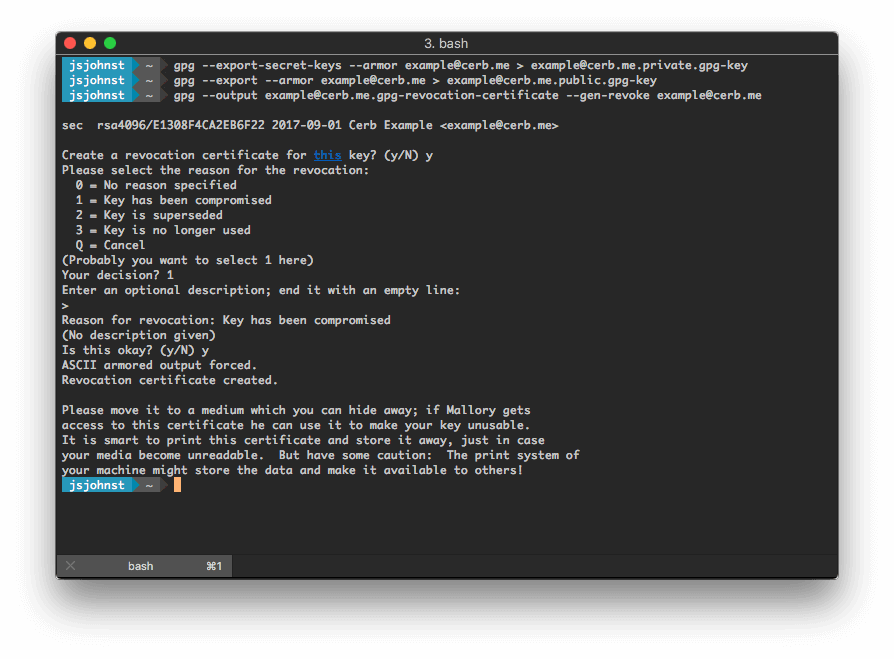
To Export just 1 specific secret key instead of all of them. Gpg -a --export-secret-keys. First you should export them.
Gpg created gpg. Keys can bei exported to files and imported on another machine. Export the data file so that it can be sent to client location for decrypting purpose.
Open Kleopatra select your own certificate click on File -. Never send your sec key via email. Option only necessary to transfer your key to another computer or create a backup in a secure location.
Keyring home user. For transferring sensitive information its enough to compress the data using the gpg utility. Secretasc export public key replace usernameemail with your email.