Zone Transfer Attack Kali

How to mitigate DNS zone transfer vulnerability.
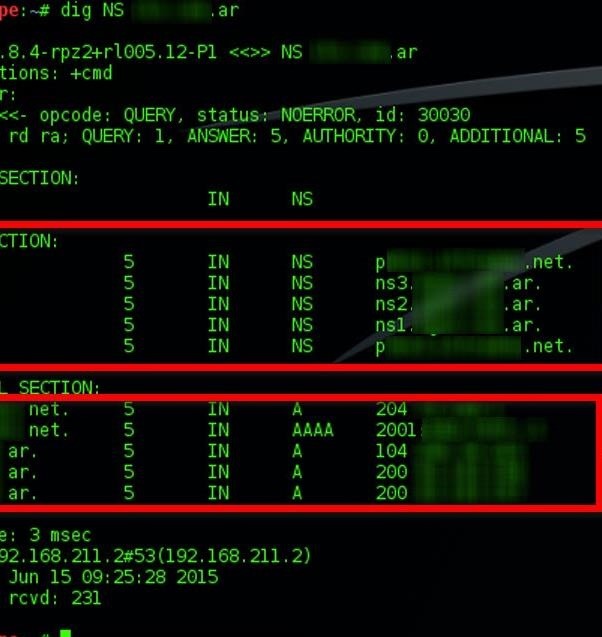
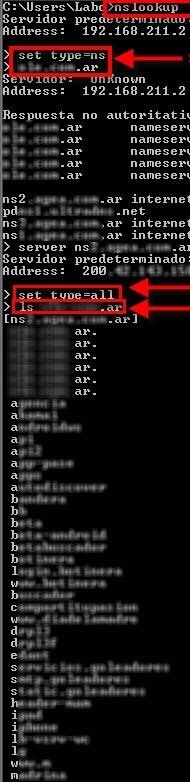
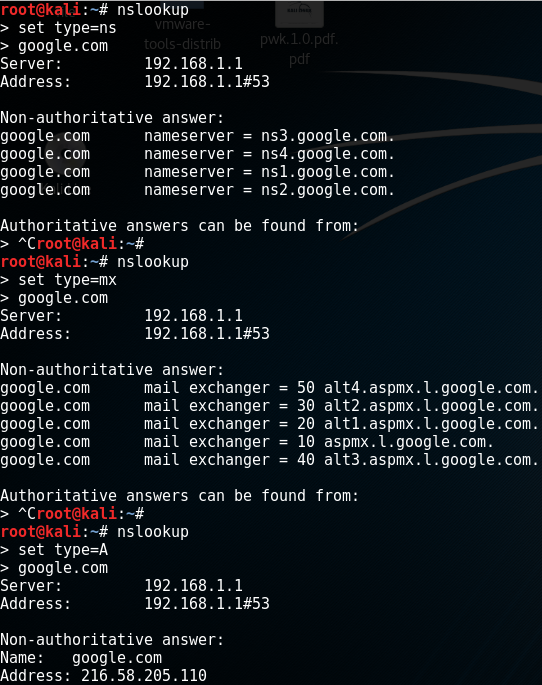
Zone transfer attack kali. Dig axfr. In this setup 1921680101 is the slave DNS server. A zone transfer uses the Transmission Control Protocol for transport and takes the form of a clientserver transaction.
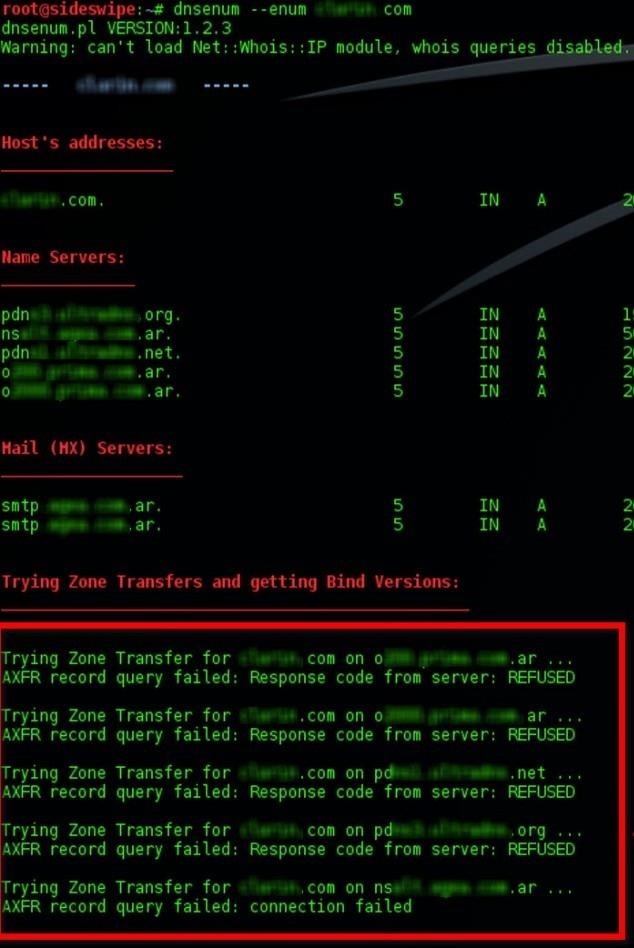
If you want to open yourself up to a zone transfer from anyone simply remove the allow-transfer line and reload bind. Top Level Domain TLD Expansion. So in our case that we have two Name Servers available we will use these commands.
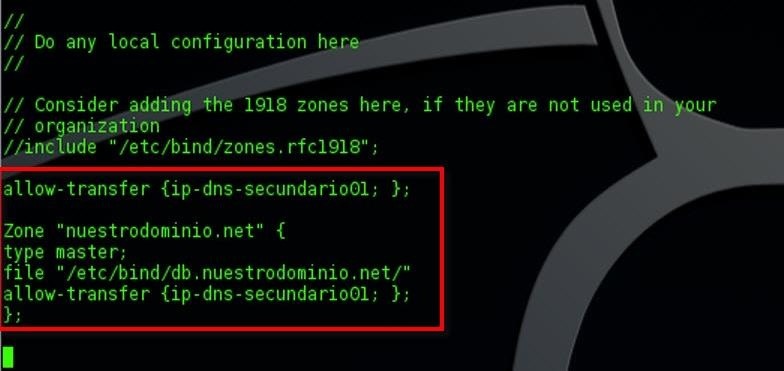
Its how you can have more than one DNS server able to answer queries about a particular zone. You can also use transaction signatures TSIG for zone transfers. Please make sure to specify the target DNS server 192XY3 while making the DNS queriesrequests.
Its like asking the nameserver Give me everything you have. DNS servers within a domain are organized using a master-slave method where the slaves get updated DNS information from the master DNS. If were talking about penetration testing DNS zone transfers are a check one is more likely to perform while.
In case of success the full zone file will be displayed. Enumerate General DNS Records for a given Domain MX SOA NS A AAAA SPF and TXT Perform common SRV Record Enumeration. To mitigate this vulnerability DNS servers should be configured by trusted IP addresses.
5 Protect DNS Zone Transfer Attack. The client requesting a zone transfer may be a slave server or secondary server requesting data from a master server or a primary server. Keep in mind that this has very little to do with web applications the above has to do with DNS.