Zone Transfer Exploit
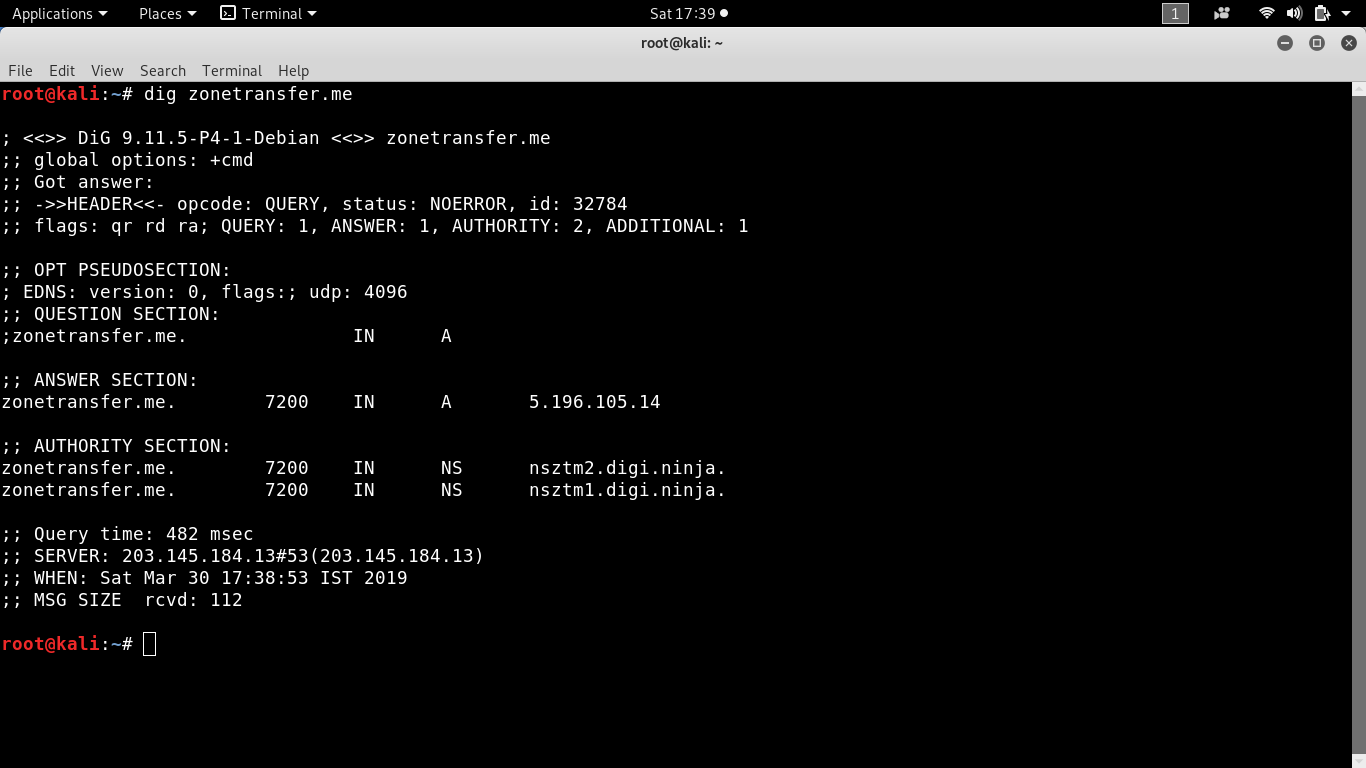
Dig axfr.
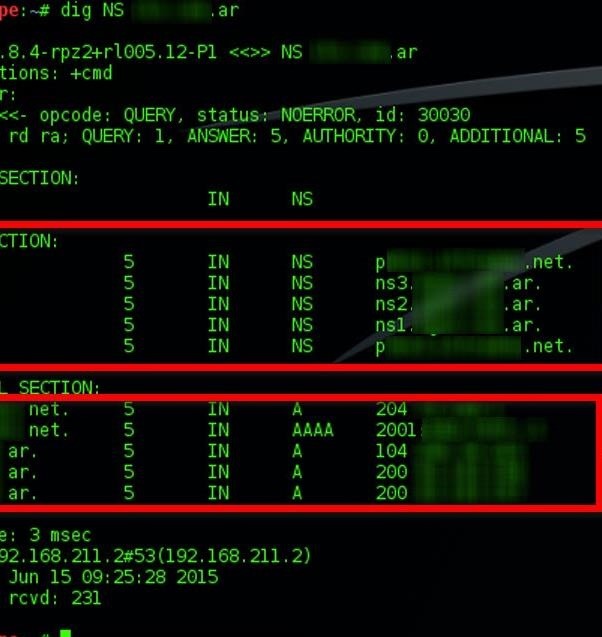
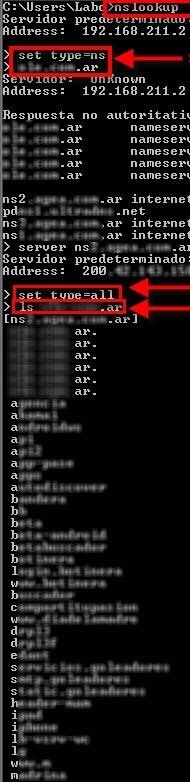
Zone transfer exploit. Nmap -vvv -Pn -sC -sV -p79 target. Requests a zone transfer AXFR from a DNS server. This is needed for redundancy.
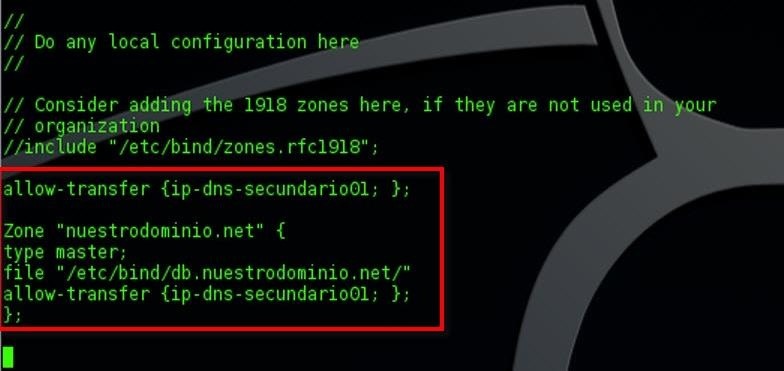
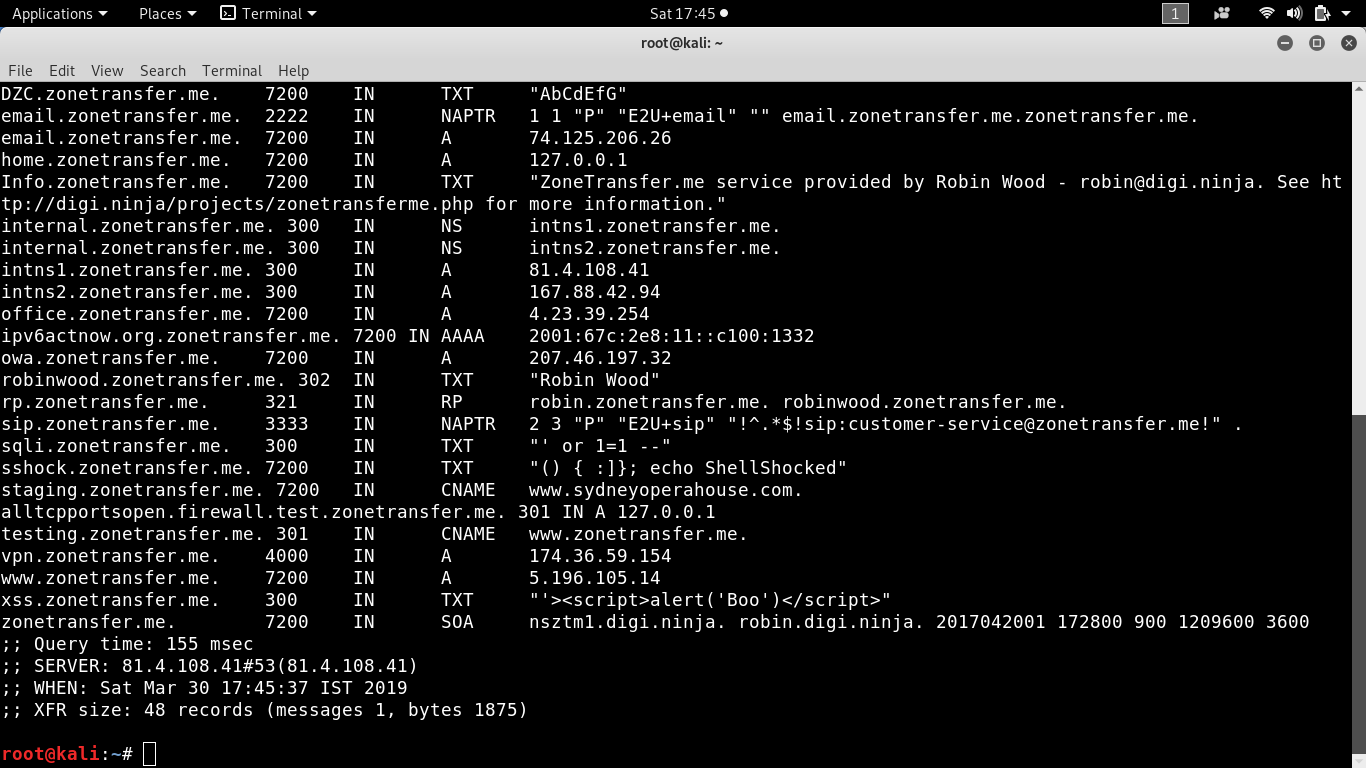
This is typically not something you want to be externally accessible. An attacker who is permitted to send zone data to a server via zone transfer can exploit this to intentionally trigger the assertion failure with a specially constructed zone denying service to. It is done to synchronize the domain records.
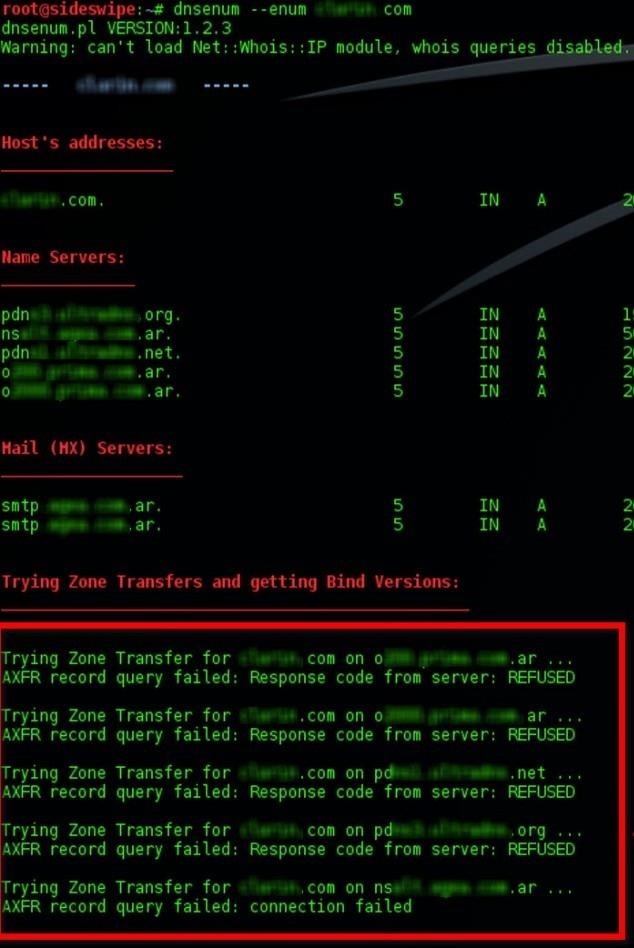
A zone transfer lets a remote attacker instantly populate a list of potential targets. Try zone transfer without domain dig axfr. Thus incremental DNS transfers were developed.
If were talking about penetration testing DNS zone transfers are a check one is more likely to perform while doing a network rather than an application pentest. Its worth stopping zone transfer attacks as a copy of your DNS zone may reveal a lot of topological information about your internal network. In particular if someone plans to subvert your DNS by poisoning or spoofing it for example theyll find having a copy of the real data very useful.
Dig ging DNS with a Zone Transfer A zone transfer that is from an external IP address is used as part of an attackers reconnaissance phase. Its like asking the nameserver Give me everything you have. DigiNinja had put up a domain name zonetransferme for testing.
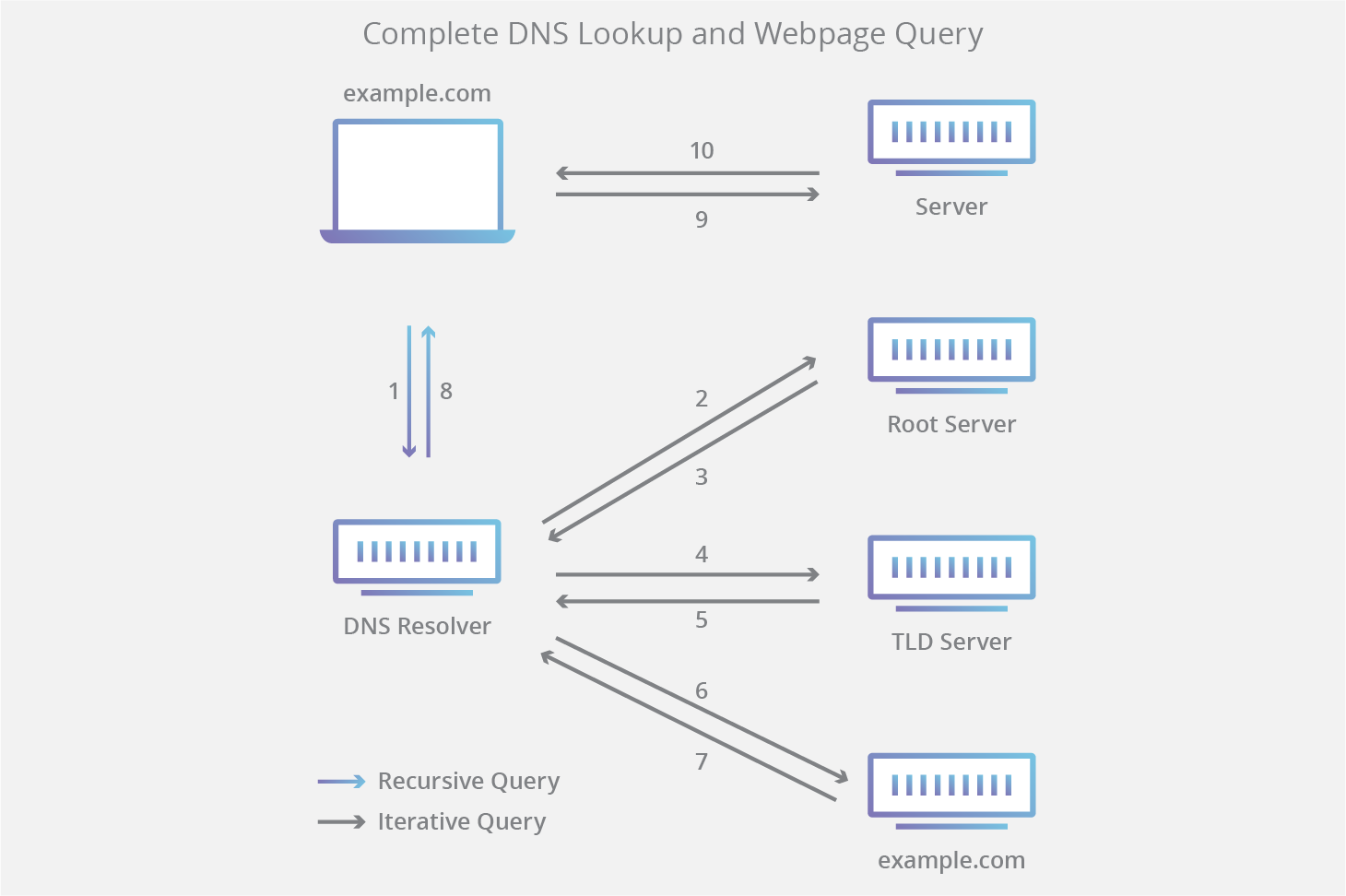
A zone transfer uses the Transmission Control Protocol for transport and takes the form of a clientserver transaction. 662020 A zone transfer is quite a normal process between two servers primary and secondary. 342021 This is basically what is called a Zone Transfer.