Transfer Public Key To Server
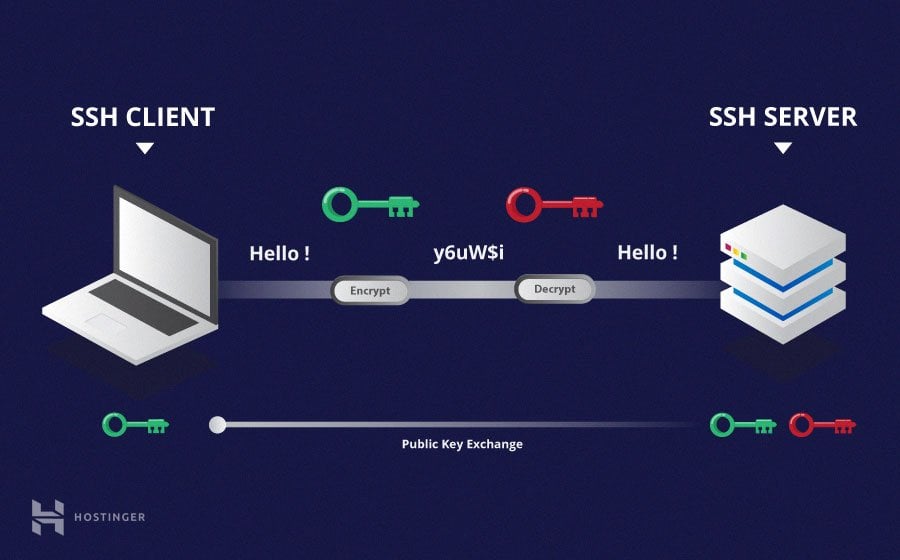
This is how the SSH client can connect to the remote server without asking you the password it only offers the public part at that point.
Transfer public key to server. The safest way to transfer the files is using scp part of ssh. 3 Associate with the user account on the User node in JSCAPE MFT Server Manager. 382019 Assuming that the public-private key pair on server_a is located in sshid_rsa you can run the following command to transfer your public key to server_b.
Scp -rp gnupg othermachine. This says the public key which you need to copy to the remote server is located in the above file. Encrypted private keys hold their corresponding public key unencrypted.
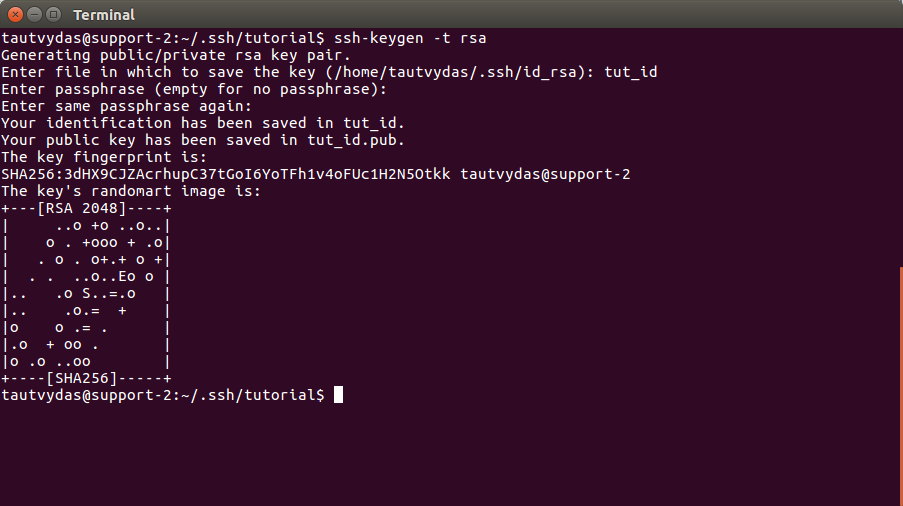
So you need to copy the content of this file and then copy or paste them in the authorized_keys of the remote server. Below command will give you the key to be copied. The first thing youll need to do is make sure youve run the keygen command to generate the keys.
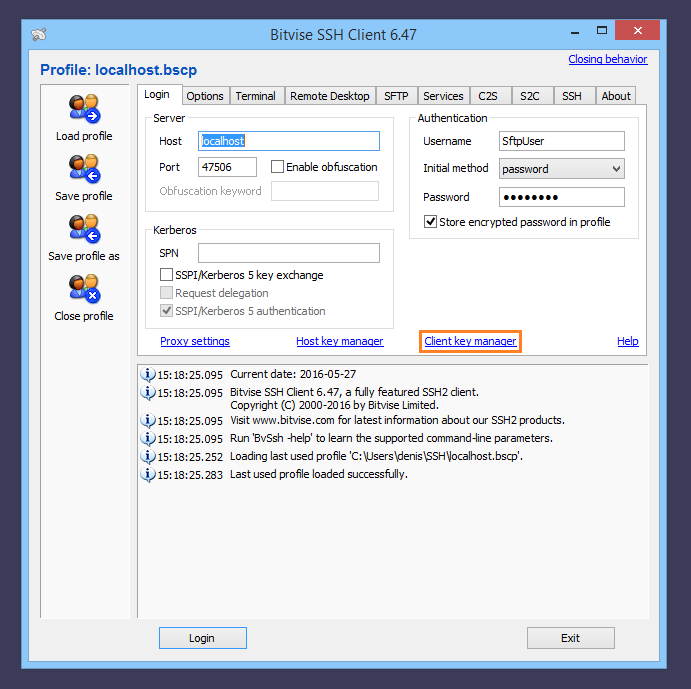
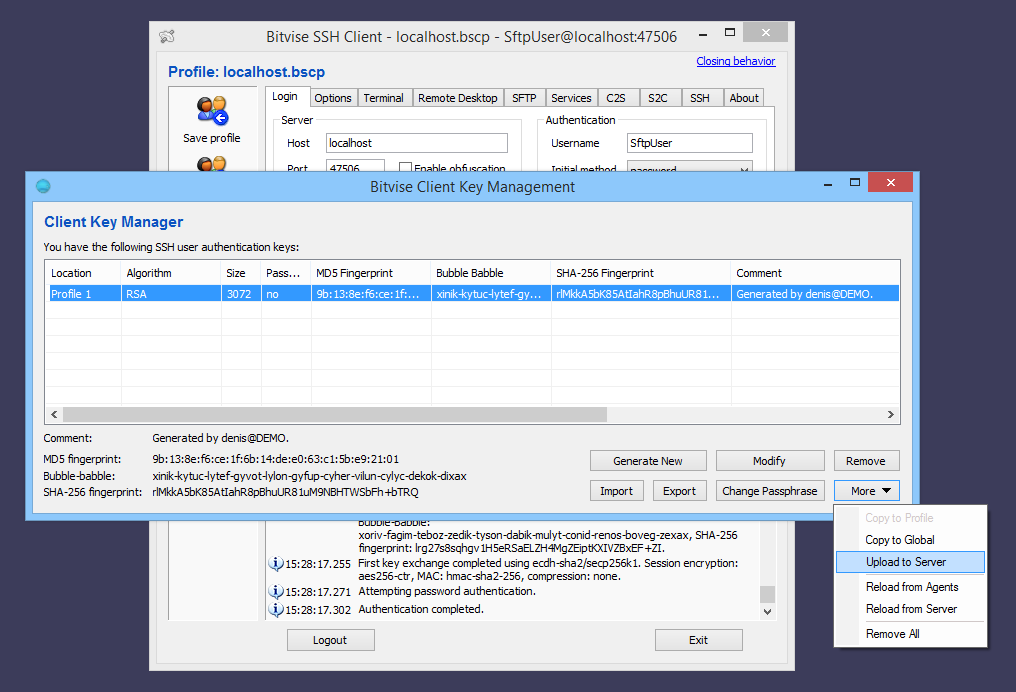
Then click Browse to select the public key file that you saved in Step 1. The public key is what you store on the server you want to connect to. Whenever the server accepts the public key the client on your PC wants to decrypt the private key and will ask you for the passphrase.
With most clients you can export the public key into a file transfer the file to the SSH Server and import it into SSH Server settings. Once an SSH key has been created the ssh-copy-id command can be used to install it as an authorized key on the server. Manually append your public key to the remote ssh servers key to authorized_keys file.
The key files are usually stored in the ssh directory. Yes you will need to transfer the keys. Import Public Key via File.