Transfer Zone With Dig

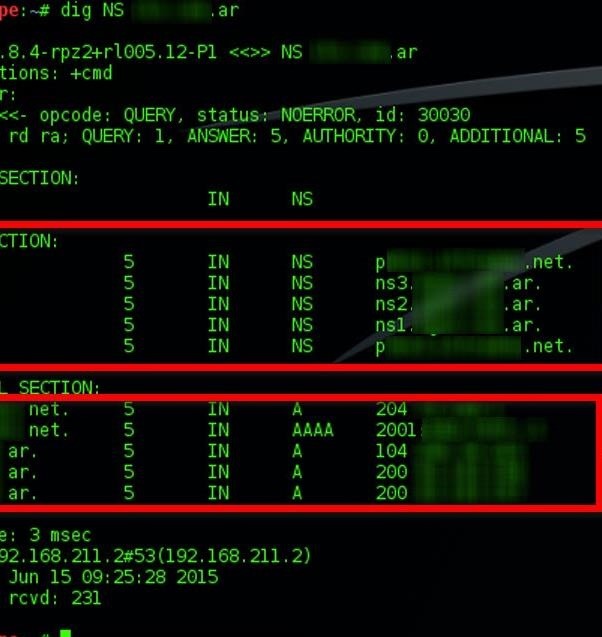
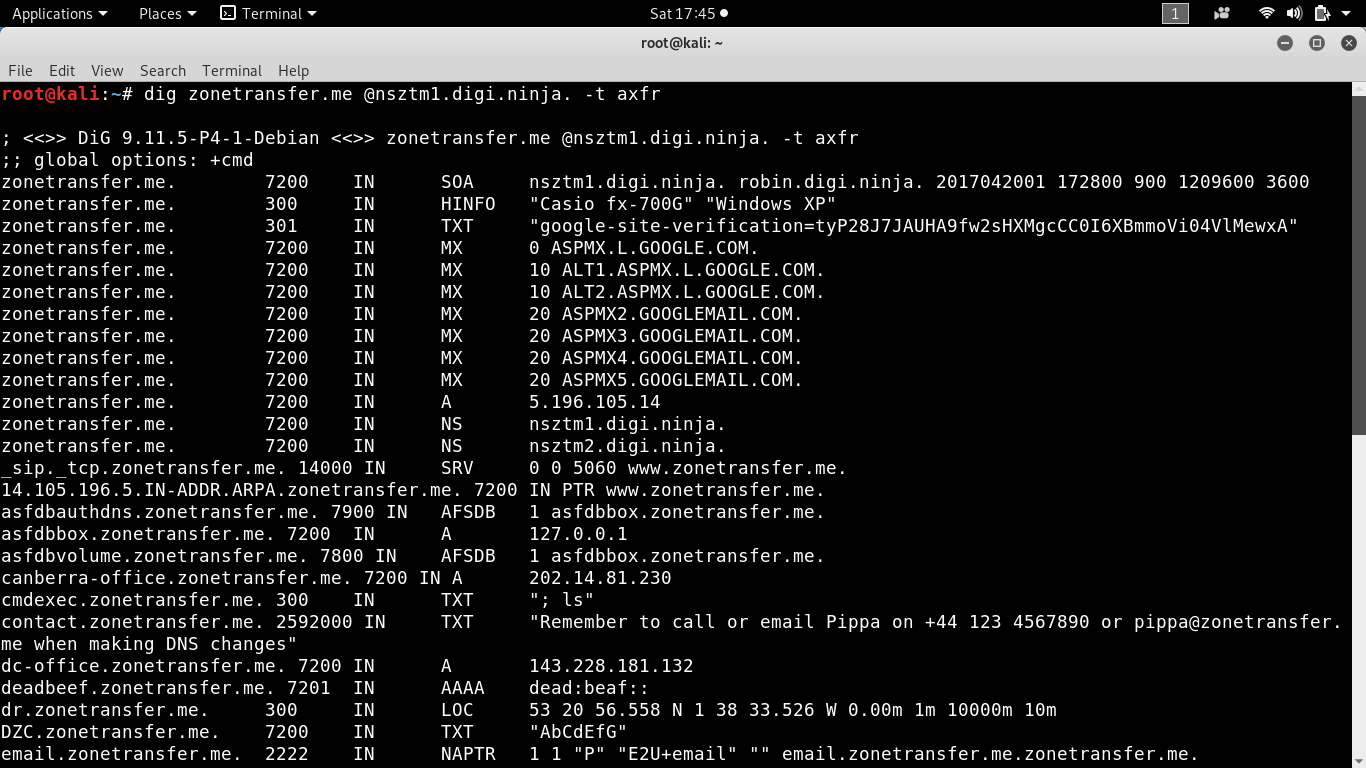
That said you can use dig to list the other records by doing.
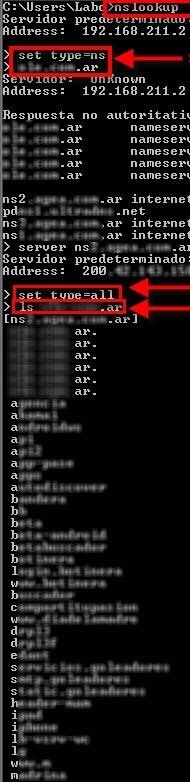
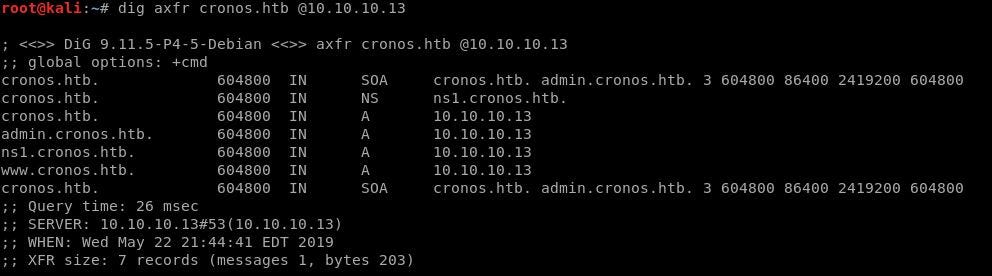
Transfer zone with dig. If were talking about penetration testing DNS zone transfers are a check one is more likely to perform while doing a network rather than an application pentest. Remember that you can only transfer a zone from a name server thats authoritative for the zone. Dig nocmd yourdomainexample any.
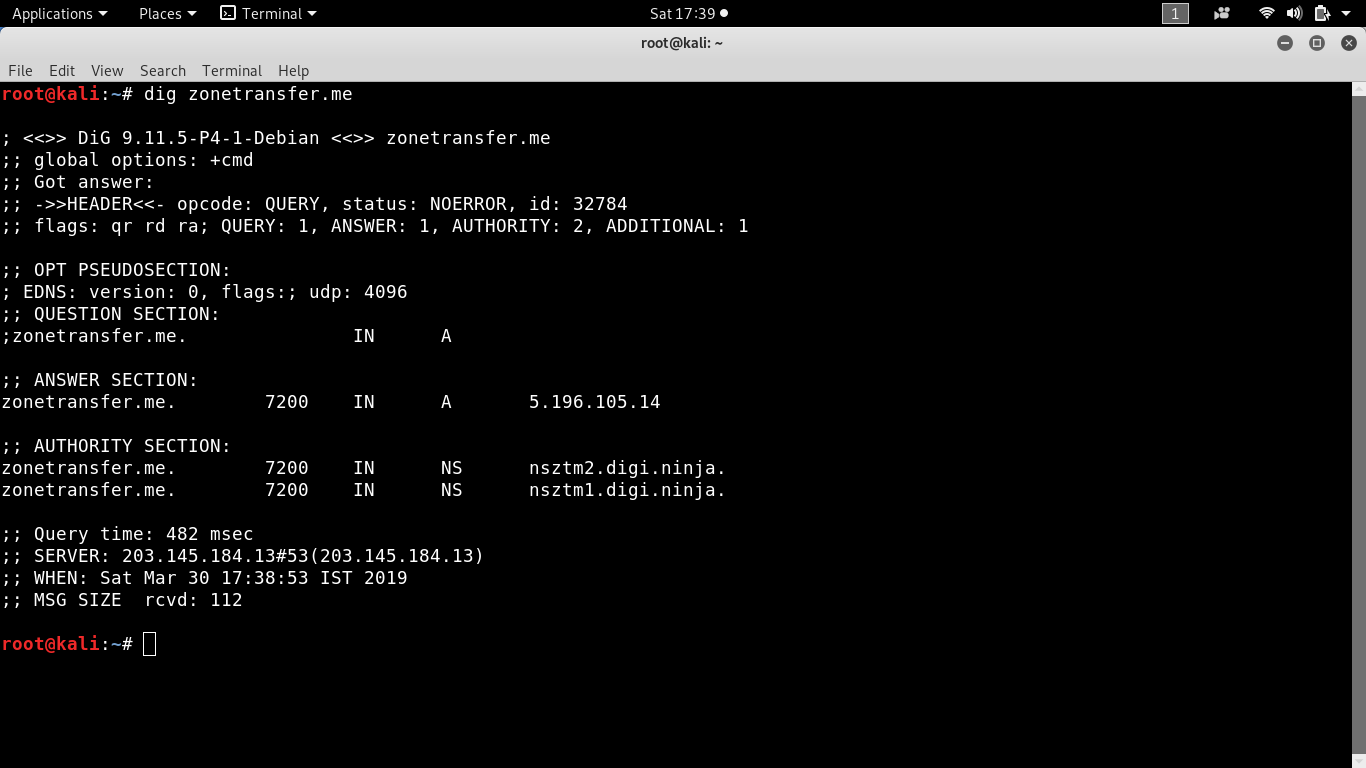
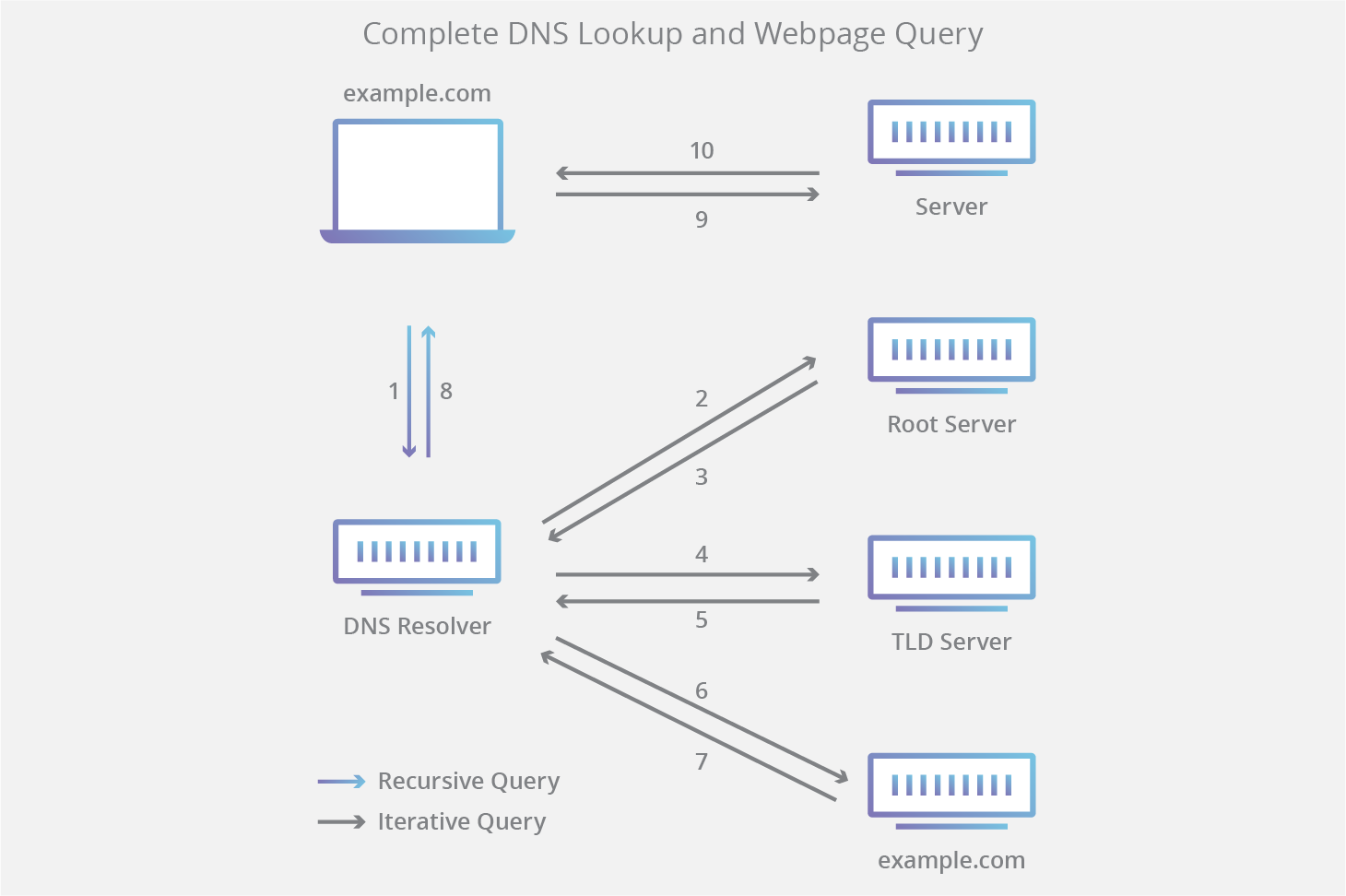
First we need to get the list of DNS servers for the domain. Dig ging DNS with a Zone Transfer A zone transfer that is from an external IP address is used as part of an attackers reconnaissance phase. The dig command will return the zone data in a text format.
352021 The Zone transfer happens when the primary DNS server dispatches a DNS zone to one of the secondary DNS servers. If successful you will be provided with a listing of all information on the nameserver from one simple command. The -t option sets the query type to type.
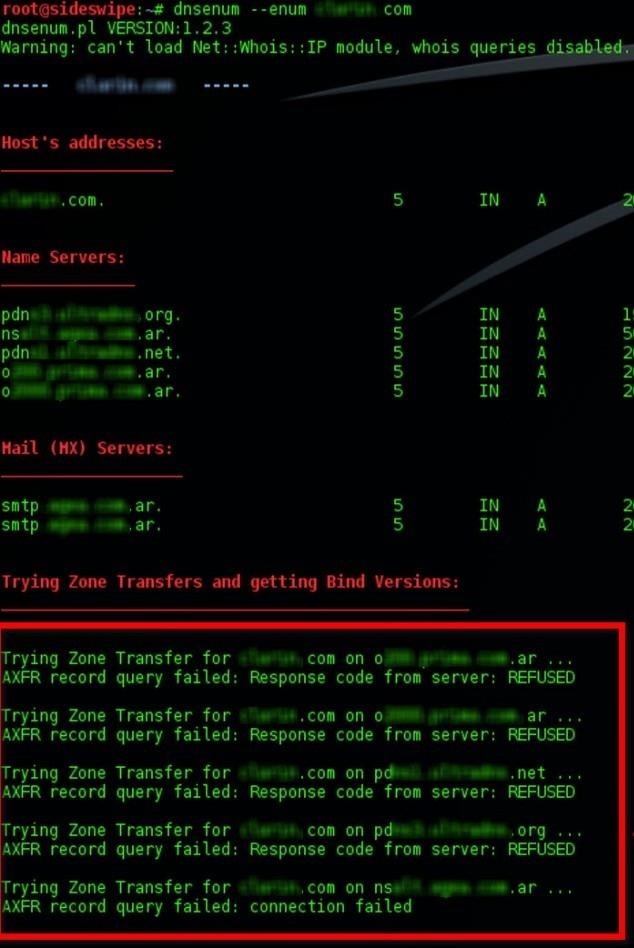
1 server found. A zone transfer can be requested by specifying a AXFR. The short answer is to your specific question of listing CNAMEs is that you cant without permission to do zone transfers see How to list all CNAME records for a given domain.
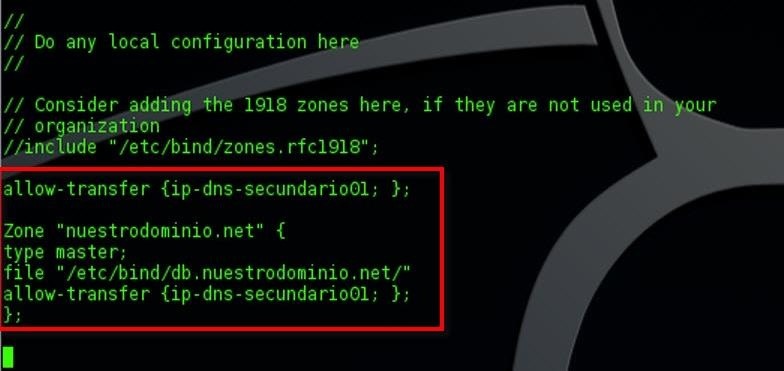
Keep in mind that this has very little to do with web applications the above has to do with DNS. This is typically not something you want to be externally accessible. Unlike nslookup though dig has no special command to request a zone transfer.
In secured environments it is highly unlikely that zone transfers are enabled as it gives an attacker a wealth of data in regards to hostnames and other informationBefore you begin. DigiNinja had put up a domain name zonetransferme for testing. Axfr nsztm1digininja zonetransferme.