Transfer Key Encryption Key

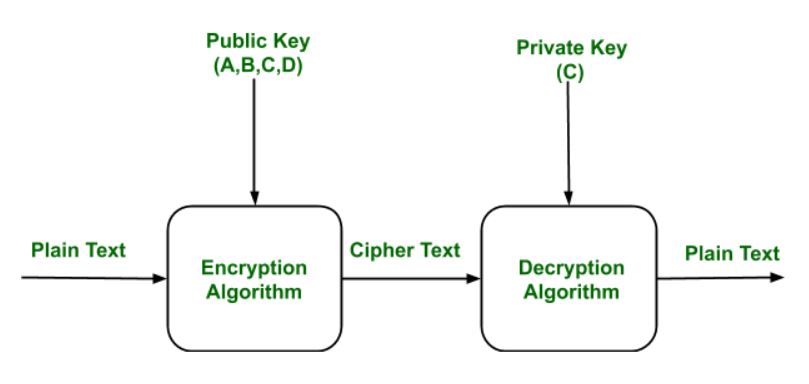
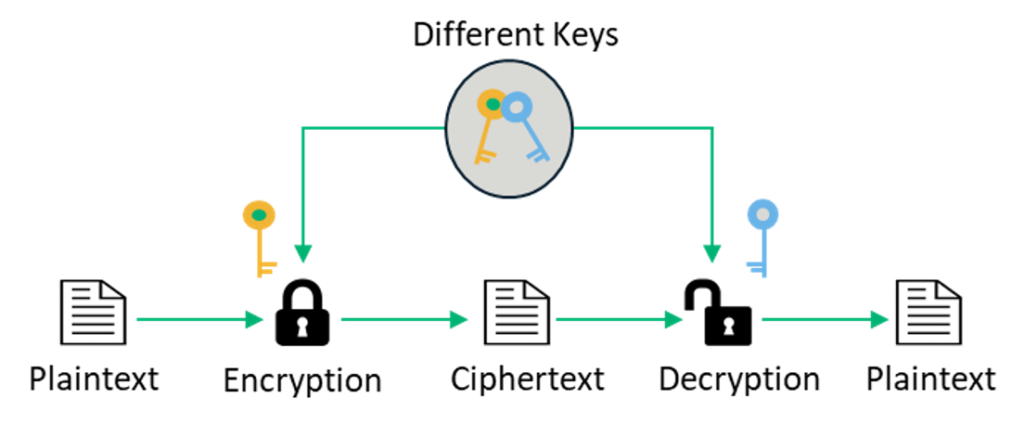
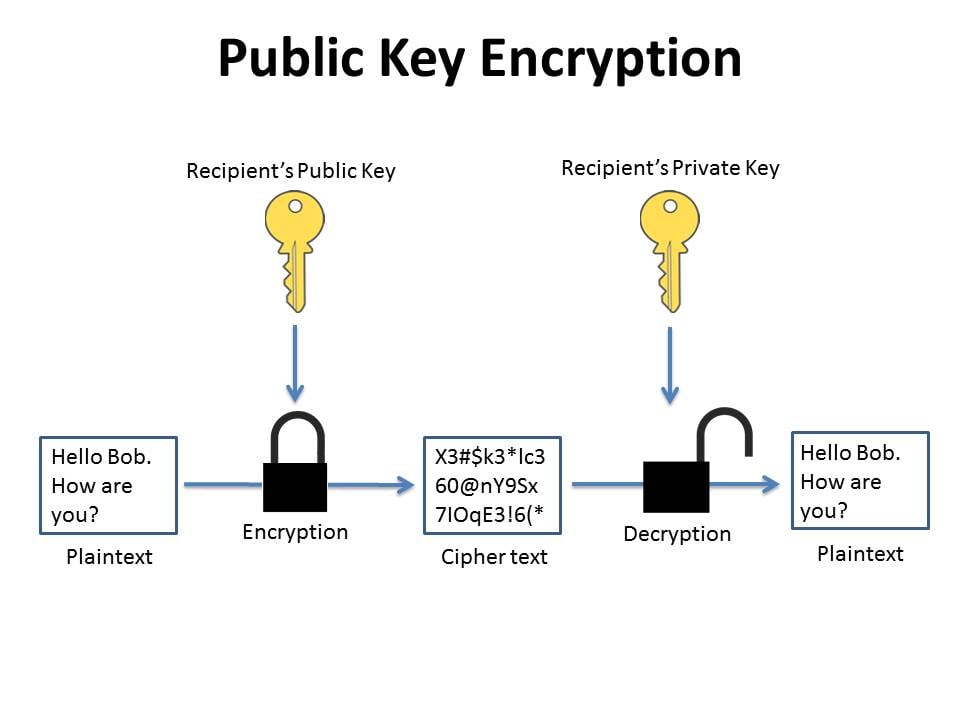
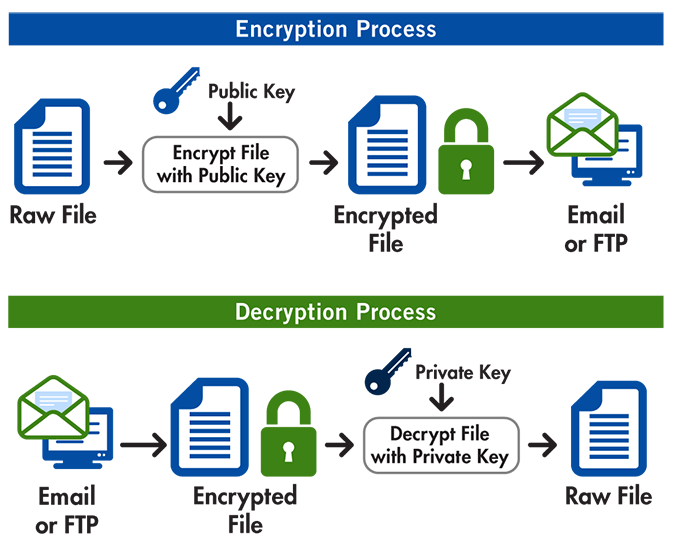
One key in the key pair is called a private key while the other one is called a public key.
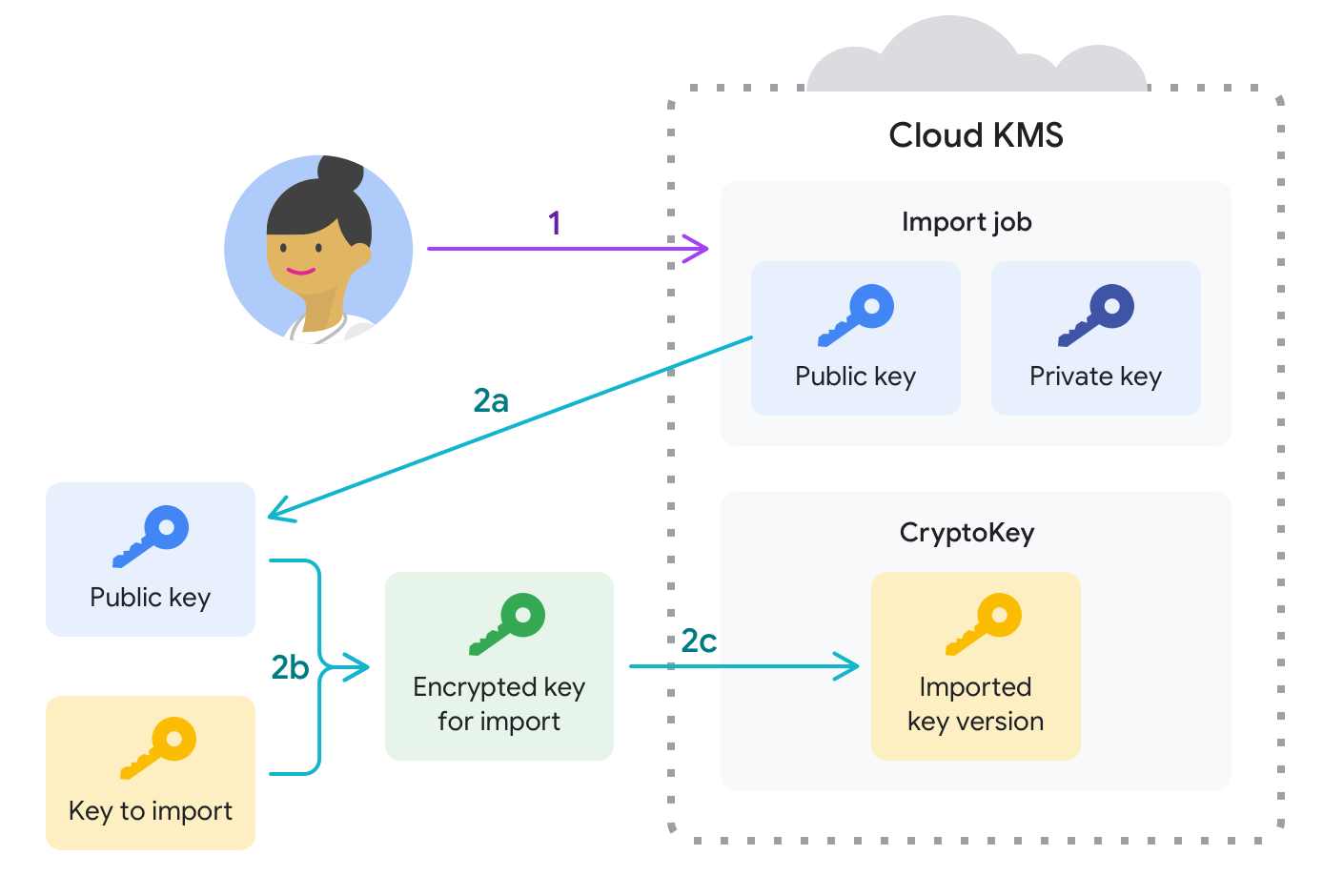
Transfer key encryption key. 1312000 Designed for Secure Data Transfer Silver Key encrypts sensitive data and creates encrypted parcel that can safely be sent over the Internet. Is an encryption key which has the function of encrypting and decrypting the DEK. The safest way to transfer the files is using scp part of ssh.
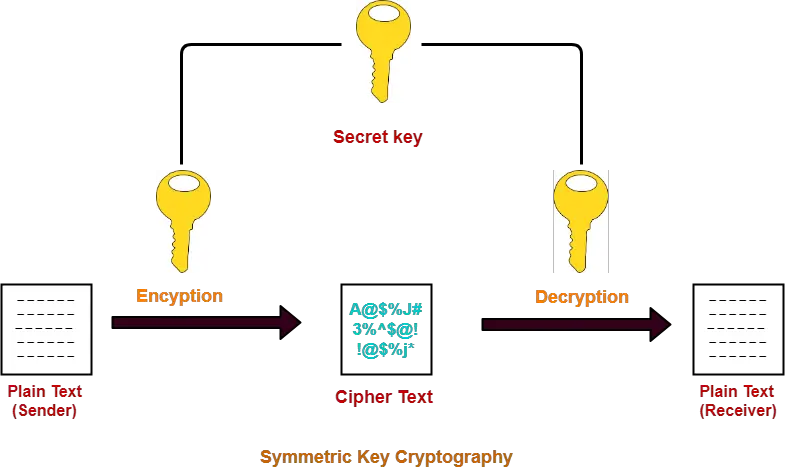
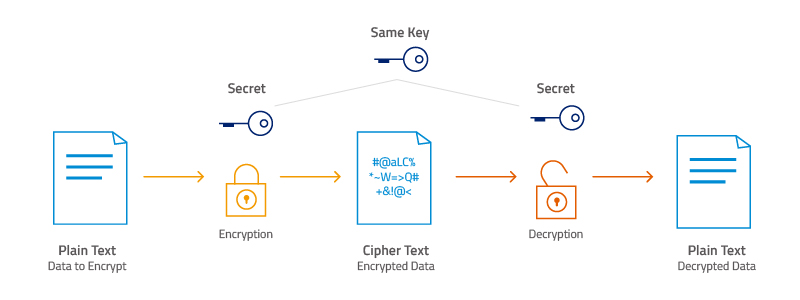
In the Password window enter the password that protects the key file and then choose OK. 12112020 AES encryption or advanced encryption standard is a type of cipher that protects the transfer of data online. The sender encrypts their message with the public key and can then send it to the recipient as cipher text.
Key that unlocks the protective encryption or a passwordpassphrase that forms the basis for the key in your possession until its time to transfer the keys you want to transfer and then decrypt them at clientss location. Key encryption key KEK. In the Select a key file to import window choose the encryption key file and then choose Open.
Public key cryptography makes use of a pair of keys. Public keys and private keys for encryption. Enter the passphrase protecting the key if applicable and click Open.
9302015 Keep the outer. In the Select a key file to import window choose the encryption key file and then choose Open. In the Password window enter the password that protects the key file and then choose OK.
Mac and Linux work the same storing the keys in gnupg. Symmetric-key algorithms use the same keys for both encryption and decryption. AES Advanced Encryption Standard Blowfish DES Data Encryption Standard Triple DES Serpent and Twofish.